🎉 Ethical Hacking Certification With 100% Internship 🎉
Get Your
Cyber Security Certificate
With 100% internship
Kickstart your cyber security career with our industry-ready training. Learn real-world tools, work on live projects, and secure a guaranteed internship to build strong hands-on experience from day one.
Get 3 Certifications with 1 Advanced Course
in just 6 Months
- DCSC – Drop Certified Security Course
- Bug Bounty & Penetration Testing
- Global-Level Ethical Hacking Certification

About Ethical Hacking Course
This ethical hacking and cybersecurity course is designed to help you understand the complete world of cyber security from scratch. Even if you have no technical background, the course guides you step-by-step to build strong, job-ready skills.
You’ll learn everything from network security, vulnerability analysis, penetration testing, bug bounty, malware & ransomware behavior, phishing attacks, exploitation techniques, reconnaissance, social engineering, and much more. Along with theory, you will also work hands-on with real tools and set up your own practice labs to gain practical experience.
The course also includes professional certification and internship assistance, helping you explore high-paying career opportunities in the cyber security industry. After completing this program, you can work as a Security Analyst, Penetration Tester, SOC Operator, Cybersecurity Consultant, Network Security Engineer, and several other roles in top IT and security companies.
Included in the Course
- Study Material
- Hands-on Training
- Hands-on Training
- Real-world Case Studies
- Career Guidance
- 1:1 Doubt Support
- Flexible Timing
- 6-Month Lab Access
- Internship & Placement Help
- Downloadable Resources
- Lab Setup Support
- Exam Guidance
Course Features
- Free Hacker's Pendrive
- Free Study Materials
- ISO Certified Certification
- Dedicated Support Team
- Highly Qualified Mentors
Tools YOU WILL MASTER
- Kali Linux
- Burpsuite Professional
- Acunetix
- Spynote (Black Edition)
- Metasploit
- Nmap
- Sqlmap
Course Duration
- 4 Months Training
- 2 Months Internship
Who this course is for
- Students with basic computer knowledge
- No coding, Linux, or prior hacking skills needed
- Anyone from 12th pass to working professionals can join
- Students curious about how cyber attacks actually happen
- Those who want to learn how to protect systems from modern threats
Step-by-Step Learning Journey
A complete, beginner-friendly syllabus covering everything from fundamentals to
advanced offensive security concepts. Designed to help you build practical skills and job-ready expertise.
Lesson 01: Introduction to Cybersecurity
Lesson 02: Introduction to Ethical Hacking
Lesson 03: Types of Cybersecurity Threats
Lesson 04: Cyber Kill Chain
Lesson 05: CIA Triad (Confidentiality, Integrity, Availability)
Lesson 06: Risk Management Fundamentals
Lesson 07: Cyber Laws and Ethics
Lesson 08: Common Vulnerabilities and Exposures (CVE)
Lesson 09: Types of Security Testing (White Box, Black Box, Gray Box)
Lesson 10: Overview of Cybersecurity Careers
Lesson 11: Offensive Security vs Defensive Security
Lesson 12: Dark Web & Deep Web
Lesson 13: Virual Box Installation(Linux,Windows)
Lesson 01: Introduction to Operating Systems
(Windows + Linux – Including How To Use It)
Lesson 02: Networking Basics(LAN, WAN, MAN)
Lesson 03: TCP/IP Model and OSI Model
Lesson 04: Common Networking Protocols (HTTP, HTTPS, FTP, SSH etc.)
Lesson 05: Network Devices (Routers, Switches, Firewalls)
Lesson 06: IP Addressing(IPV4, IPV6),Ping,Traceroute
Lesson 07: Hardware Hacking Tools
Lesson 08: Virtual Private Networks (VPNs)
Lesson 09: Domain Name System
Lesson 10: How Internet Works(Request, Respons, Cookies)
Lesson 11: TCP VS UDР
Lesson 12: Nmap, Zenmap
Lesson 13: IDS VS IPS
Lesson 01: Introduction to Footprinting
Lesson 02: Tools for Footprinting (WHOIS, Wappalyzer, Wayback Machine)Lesson 03: Tools for Footprinting (Shodan, Address Resolution Protocol, Eaves Dropping)
Lesson 04: Tools for Footprinting (HTTrack, CMS Enemuration,
OSINT Framework)
Lesson 05: Tools for Footprinting (Google Dorks)
Lesson 01: Android Hacking by Remote Access Trojan
Lesson 02: System Hacking by Remote Access Trojan
Lesson 03: MSFVenom
Lesson 04: Windows Defender Bypass
Lesson 05: File Extension Spoofer
Lesson 06: Silent Exploit
Lesson 07: Cookie Stealing Attack
Lesson 01: Introduction to Web Application Security
Lesson 02: OWASP Top Ten Vulnerabilities
Lesson 03: Burp Suite Training
Lesson 04: WpScan
Lesson 05: Cross-Site Request Forgery (CSRF)
Lesson 06: IDOR
Lesson 07: Price Tempring
Lesson 08: Brute Force
Lesson 09: ОТР Вурass
Lesson 10: Full Path Disclosure
Lesson 11: Exploit DB
Lesson 12: XSS
Lesson 13: Clickjacking
Lesson 14: POC
Lesson 01: Introduction to Malware (Viruses, Worms, Trojans)
Lesson 02: Phishing Attacks Or Social Engineering
Lesson 03: Camphish
Lesson 04: Denial of Service (DoS) and DDoS
Lesson 05: SQL Injection
Lesson 06: Wireless Network Attacks
Lesson 07: WIFI Jamming | WIFI DOS
Lesson 08: WiFi Hacking |
Lesson 09: Sniffing
WIFI Phishing
Lesson 01: Introduction to Cryptography
Lesson 02: Hashing
Module 08 : LinkedIn
Module 09 : Resume Building
Why This Program?
A beginner-friendly, fully practical cyber security program designed to help you learn real skills, work on real attacks, and build a strong foundation for your career.
- Learn from industry experts
- 100% practical-based learning
- Real-world projects & labs
- Beginner-friendly curriculum
- Job-oriented skill development
Start Learning
Understand networking, OS, Linux basics, and essential cyber concepts.
Build Real Skills
Perform footprinting, scanning, vulnerabilities, exploits, OSINT, etc.
Work on Real Attacks
Practice penetration testing, bug bounty tasks, and live labs.
Become Job-Ready
Get placement support, create your cyber portfolio, and start your career.
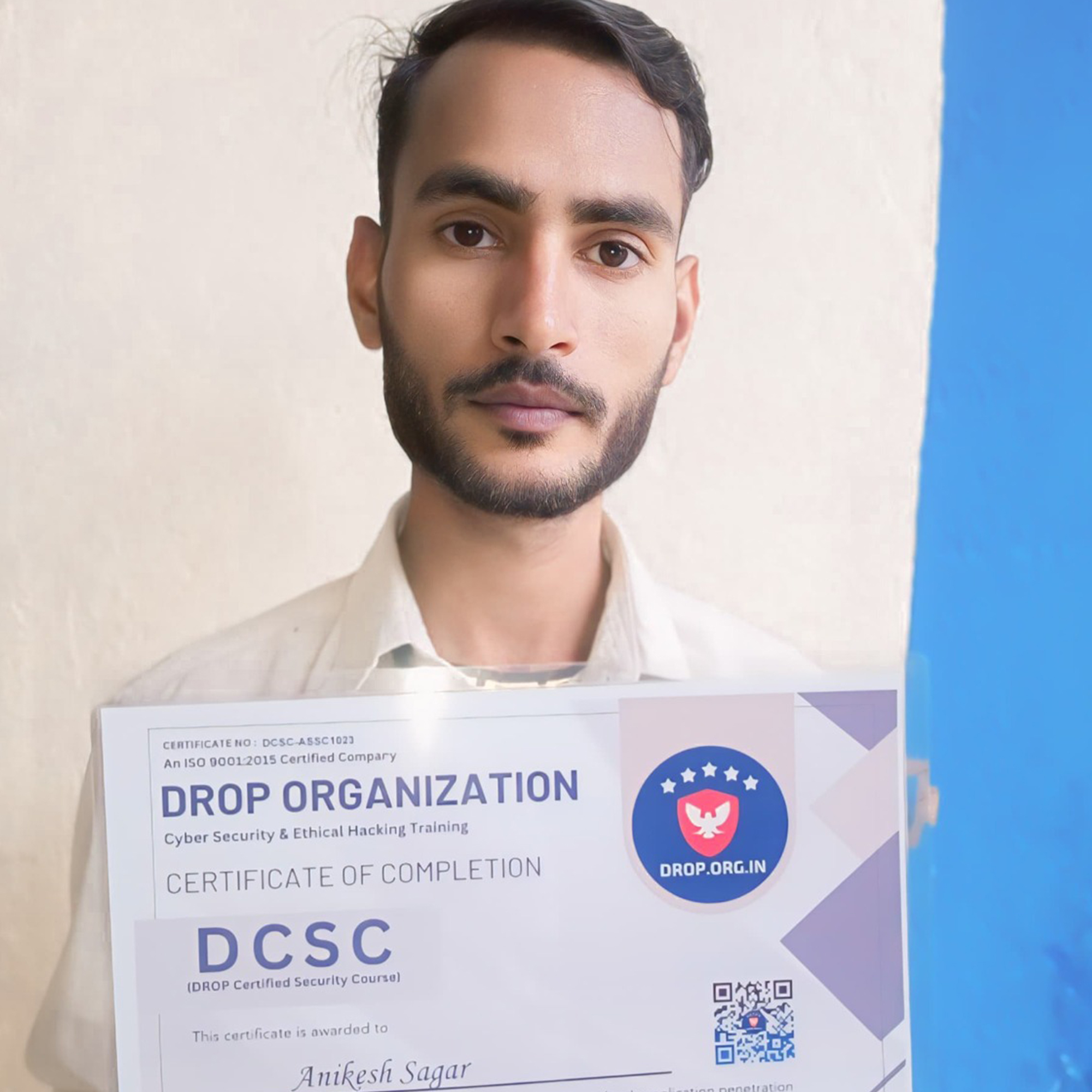
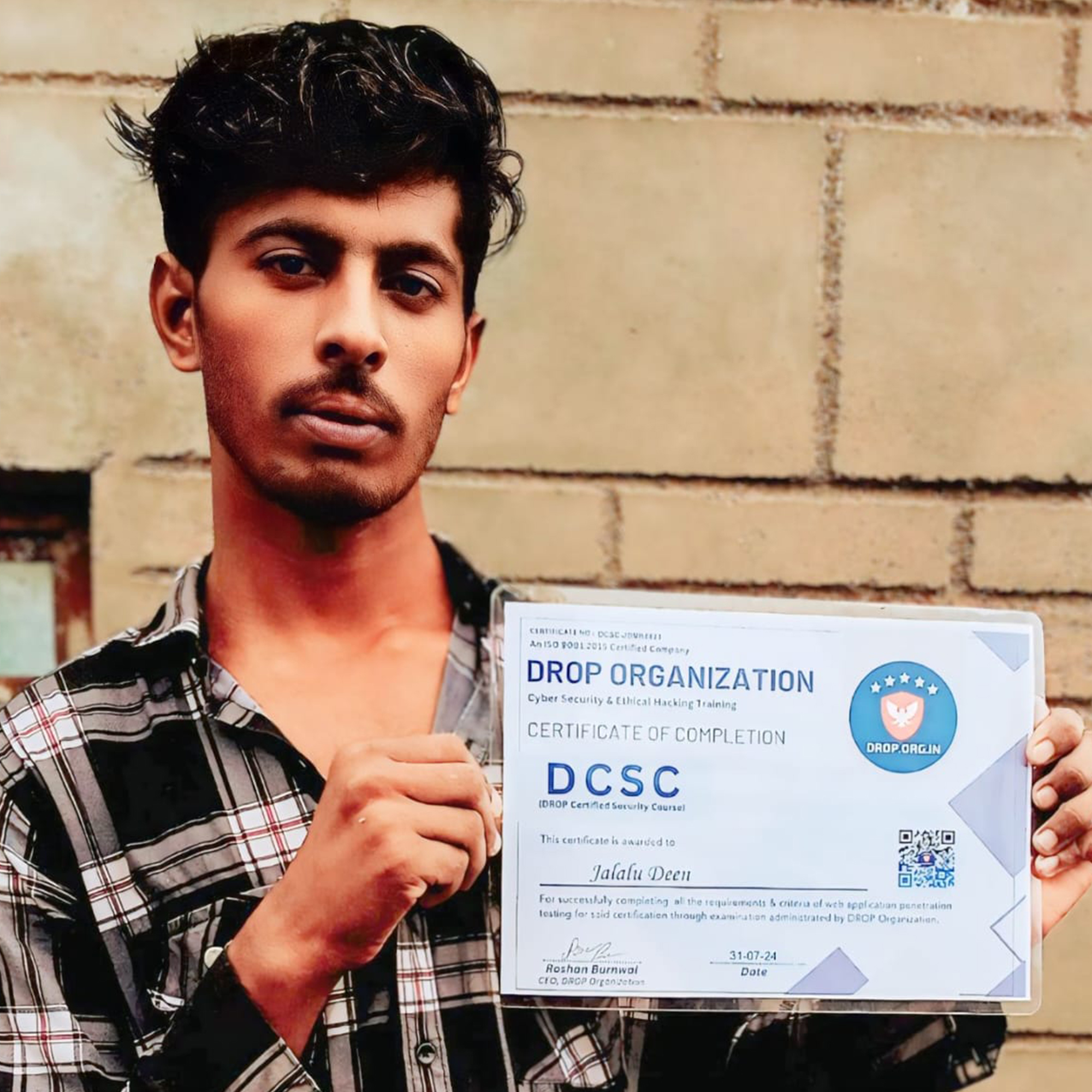
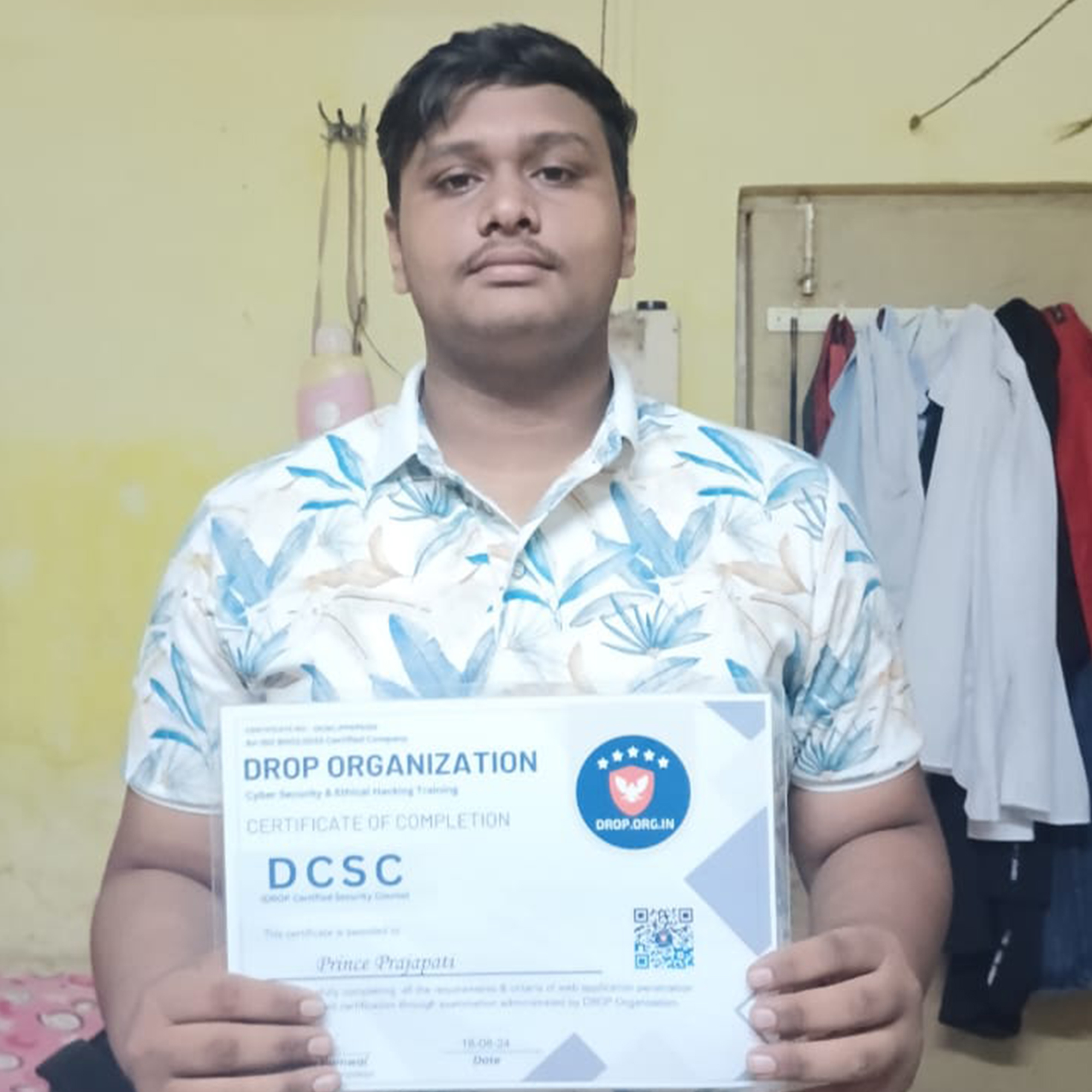
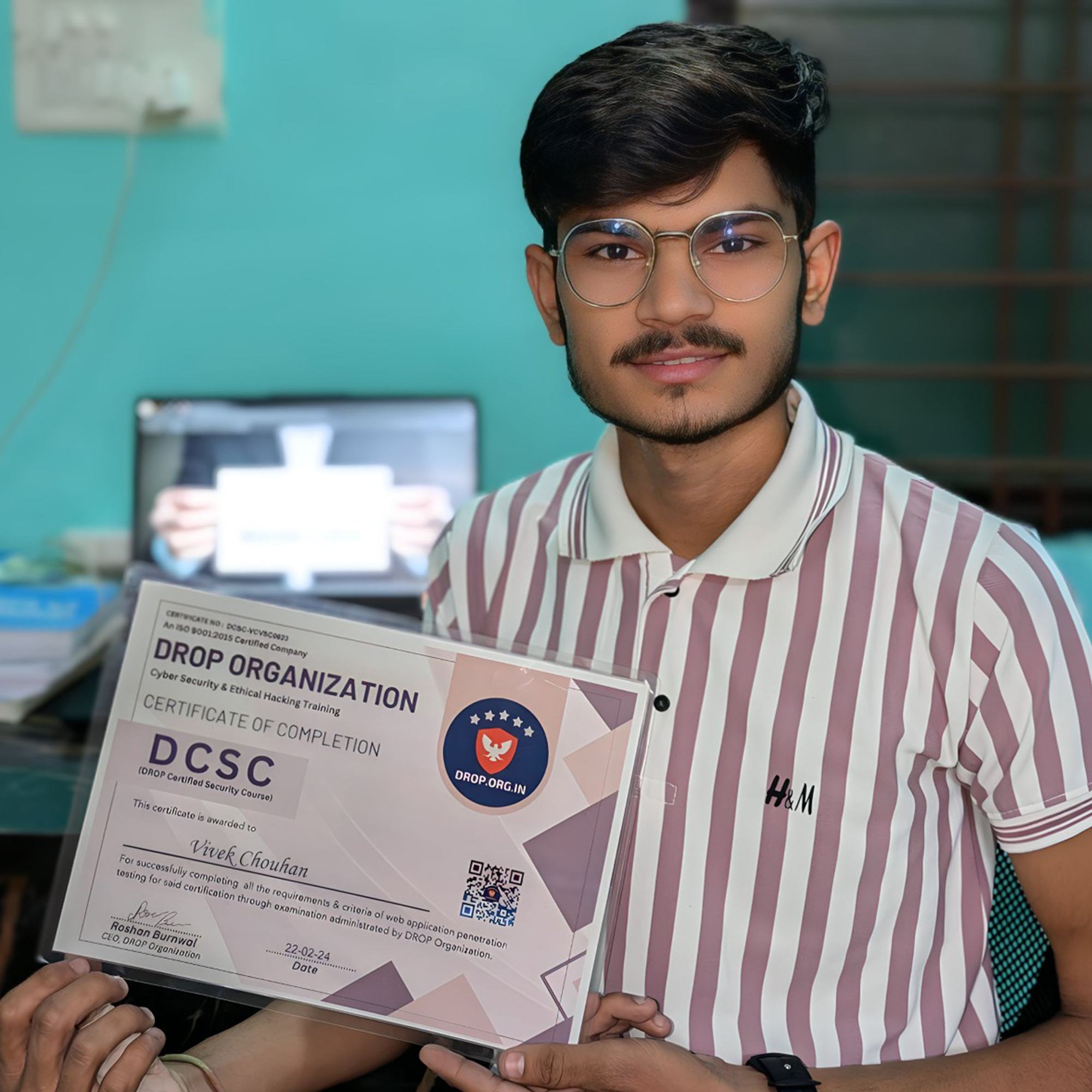
Students who are already certified
Students who have successfully completed the course and earned globally recognized certifications.











START YOUR LEARNING JOURNEY
Unlock the skills that shape the future of cyber security. Step-by-step guidance, hands-on labs, and real-world learning—start growing your expertise from Day 1